What is LoRaWAN® and how does it work?
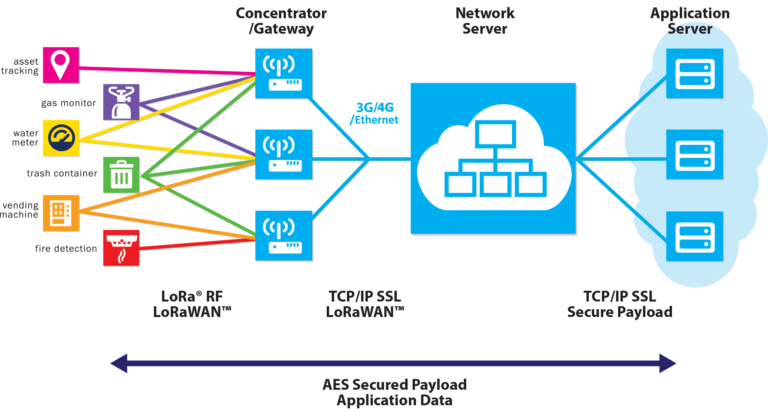
LoRaWAN®: Long Range Wide Area Network, is a protocol developed by the LoRa Alliance.
The peculiarity of this new protocol is the efficiency; because LoRaWAN® has the minimal power consumption, long range of communication (up to 15km in rural areas) and secure data transmission (with AES-128 encryption).
The range of communication is around 2km in dense urban area, up to 15km in the rural areas and is influenced by the position of the end device and of the gateway, if the gateway is mounted in an high place the cover will be major than if is mounted in a low place.
LoRaWAN® is part of a bigger category of technologies named LPWAN, that stands for Low Power Wide Area Network, this technology was born for the necessity of sending and receiving messages from sensor that operate on battery, using the smallest amount of energy available to preserve the battery energy.
Technical specifications
LoRaWAN® supports three different class of devices: Class A, Class B, Class C.
Class A devices are battery powered, when an uplink is sent to the server the device open two short downlink windows for eventual commands, if the server cannot send a downlink communication in these two short windows, it will have to wait till the next uplink message.
Class B devices are battery powered, in addition to the two short windows of Class A, Class B have an extra downlink windows that is opened at scheduled times. This windows is synchronized with the server using a Beacon from the gateway and allows the server to know when the end device is listening.
Class C devices are electrically powered, the receive windows are nearly continuously open, only during transmission are closed.

Sicurezza della rete LoRaWAN®
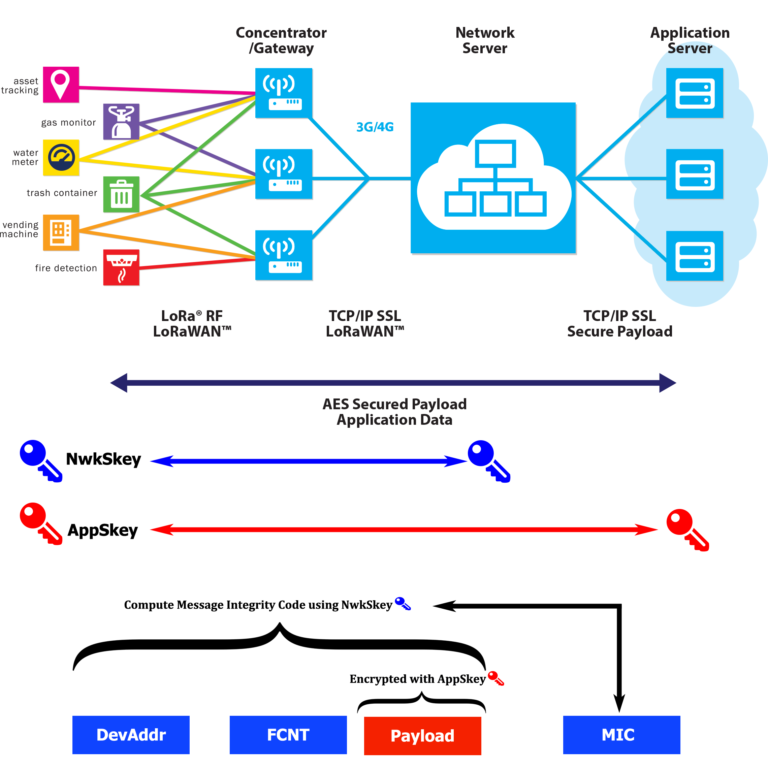
LoRaWAN® uses two types of symmetric session key for the security of the communication, that are unique for each LoRa device. The NwkSkey is used to guarantee the message integrity from the device to the LoRa Network Server. The AppSkey is used for the end-to-end AES-128 encryption from the device to the Application Server.
LoRaWAN® devices have two ways to join the network. The first is OTAA, Over-the-Air-Activation. The device and the network exchange a 128-bit AppKey. When the device send the join request, the AppKey is used to create a Message Integrity Code (MIC), the server then check the MIC with the AppKey. If the check is valid, the server creates two new 128-bit keys, the App Session key (AppSkey) and the Network Session Key (NwkSkey). These keys are sent back to the device using the AppKey as an encryption key. When the keys are received the device decrypts and installs the two session keys.
The second method for the network join is ABP, Activation by Personalization. In this case the device session keys are inserted by the user, thus is possible to have security issues.
LoRaWAN® Applications
ISM Frequency Bands
- AS 923MHz
- AU 915-928MHz
- CN 470-510MHz
- CN 779-787MHz
- EU 433MHz
- EU 863-870MHz
- IN 865-869MHz
- KR 920-926MHz
- US 902-928MHz